Adopting a Zero Trust approach is a technology and business imperative
This infographic provides an easy-to-understand overiew of the benefits of a zero trust strategy for your cybersecurity. Zero trust is a “never trust, always verify” strategy to ensures cyber-thieves can’t easily gain entrance to your data and applications, even if they have stolen credentials. How does it work? Get this infographic.
View: Adopting a Zero Trust approach is a technology and business imperative
Recent Posts
Lexmark digitally transforms its service organization
April 10, 2025
Lexmark found it could reduce agent handling time in its call centers by 25 percent, create optimized service dispatch routes and improve technician efficiency by 20 percent. Read this customer story showing how they used @Microsoft Azure IoT to get a 360-degree view of their operations and complete a digital transformation that brings long-term success for their customers, partners and employees.
Read More
New Copilot enhancements help small and medium-sized businesses innovate
April 9, 2025
AI keeps getting smarter. 🧠 Microsoft has rolled out new enhancements to Copilot, helping your team streamline workflows, boost efficiency, and stay competitive. Read the blog to see how Copilot's latest improvements can help your team work smarter.
Read More
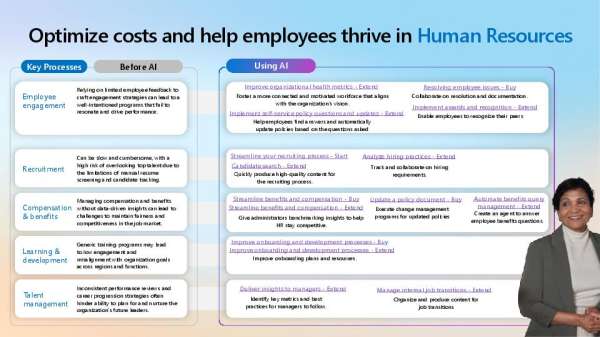
Using Copilot to Optimize HR Costs & Help Employees Thrive
April 9, 2025
Is your HR team struggling to balance cost efficiency with employee satisfaction? @Microsoft Copilot helps HR teams make data-driven decisions, optimize hiring and benefits management, and improve workplace engagement — all while reducing costs. View the infographic to see how #AI is changing HR for the better.
Read More