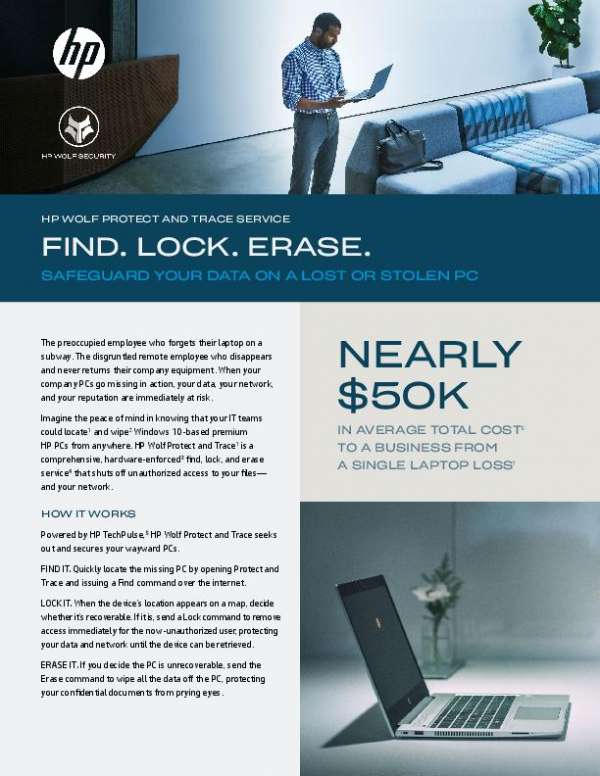
HP Wolf Protect and Trace Service. Find. Lock. Erase.
This solution brief explains how HP Wolf Protect and Trace works and lists 3 ways the solution helps keep a business’s data out of the wrong hands. Contact Hynes Group, LLC today for more information about HP Wolf Protect and Trace!
View: HP Wolf Protect and Trace Service. Find. Lock. Erase.
Recent Posts
The Modern Threat Actor’s Playbook
April 3, 2025
Ransomware attackers are targeting credentials, browsers, and unmanaged endpoints more than ever. What are you doing to stay prepared? 🔐 Download this report from @eSentire Threat Response Unit, which reveals key trends and offers expert recommendations to help you develop stronger ransomware resilience.
Read More
The superpower behind AI is you
April 2, 2025
Creativity can't be automated but #AI can elevate it. 💡 This eBook shows how blending human expertise with AI tools streamlines workflows, boosts productivity, and fuels innovation. Download your copy to kickstart your AI journey. Ready to explore what's possible? Reply below and we'll be in touch. @HP
Read More
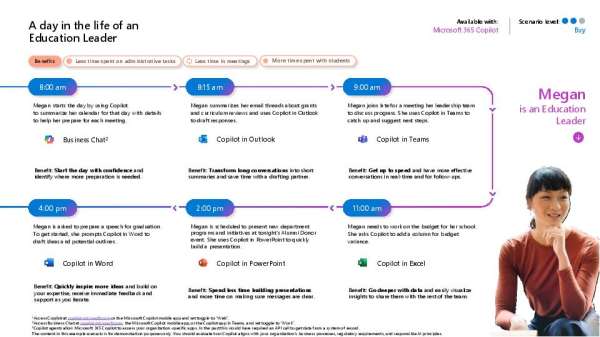
A day in the life as a K-12 educator (2)
April 2, 2025
📣 Education leaders: How do you balance meetings, budgets, and strategic planning? @Microsoft Copilot helps streamline your daily tasks so you can focus on what matters most... supporting students. View the infographic to see a day in the life of an education leader using Copilot, highlighting time-saving #AI features for communication, budgeting, and decision-making.
Read More